Phishing
What is Phishing?
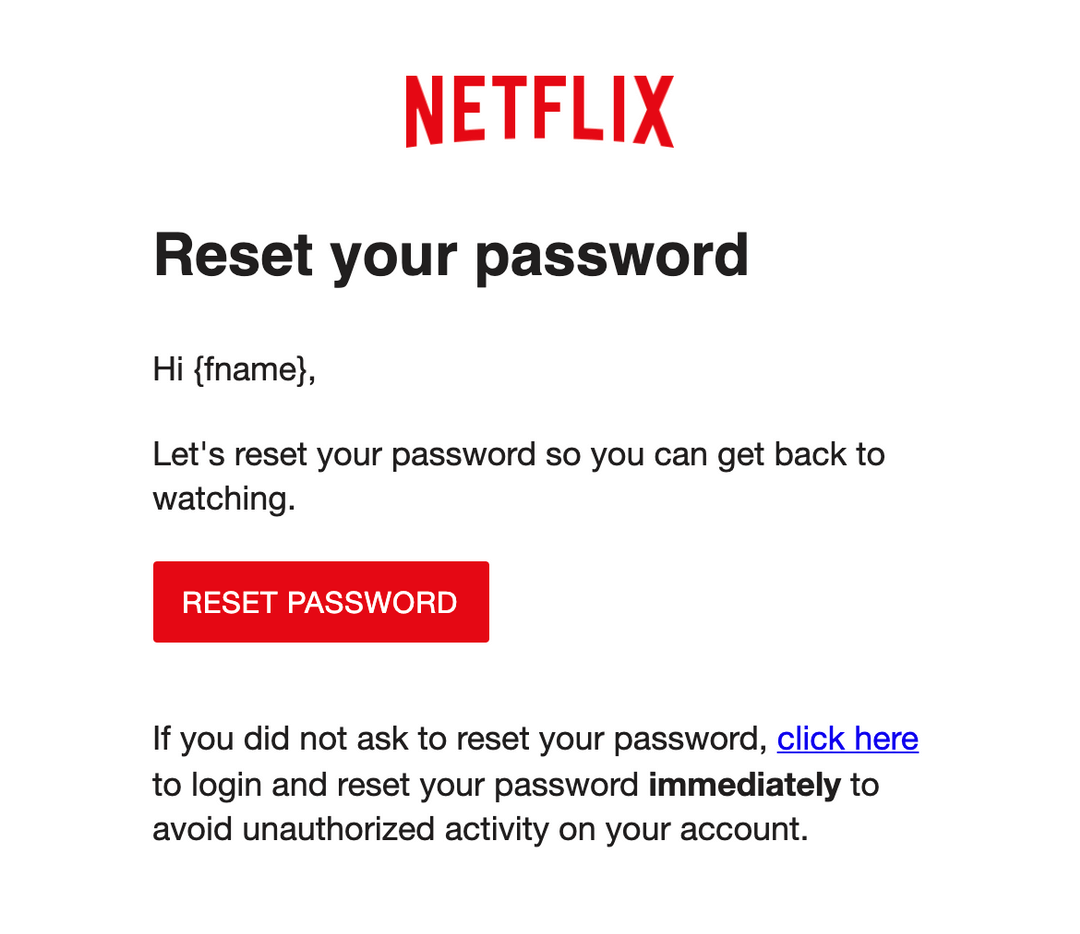
Phishing is a social engineering attack that tricks people into revealing sensitive information, opening malicious content, sending money, or taking unsafe actions by pretending to be a trusted source.
Examples
- An employee receives an email that looks like it came from Microsoft and is urged to sign in immediately to fix a mailbox problem, but the link leads to a fake login page.
- A user gets a message that appears to be from their bank asking them to confirm account details, and the attacker uses the submitted information to steal money.
Discover 🔎
Phishing remains one of the most common and effective cyber threats because it targets people directly. Attackers do not always need to break through firewalls or discover advanced software flaws if they can simply persuade someone to click, trust, or respond. That is what makes phishing so dangerous. It turns ordinary communication into an attack path.
Most people think of phishing as fake emails asking for passwords, but the threat is broader than that. A phishing message may try to steal credentials, deliver malware, trick someone into sending money, or convince them to reveal internal information. The message often looks routine at first glance, which is why it succeeds so often. It blends into normal business activity and counts on the target reacting quickly instead of carefully.
Summary 📝
Phishing is a social engineering attack that uses trust and deception to make people reveal information or take harmful actions. It is dangerous because it can lead to credential theft, malware infection, fraud, and larger security compromise. Strong defense combines email protections, user awareness, verification habits, and controls that reduce the impact if an attack succeeds.
Tip: The interactive version includes progress tracking, decks, and premium deep dives.